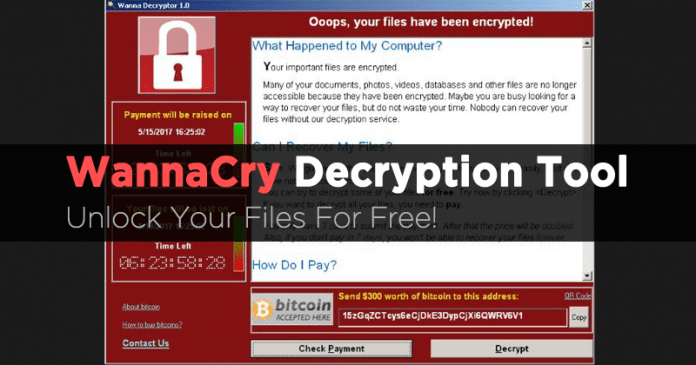
Free WannaCry Ransomware Decryption Tool Released! Unlock Files For Free
The malicious software WanaCryptor 2.0 which is also known as WCry is now being used to carry out one of the biggest ransomware attacks of its kind. The security researcher who goes by the name Benjamin Delpy has created another tool can unlock the locked computer.
Free WannaCry Ransomware Decryption Tool Released! Unlock Files For Free
Earlier this year the hacking group ‘The Shadow Brokers’ chose to give away the hacking tools that were stolen from the NSA for free. Well, the tools can be utilized to hack machines running on Microsoft Windows.
The malicious software WanaCryptor 2.0 which is also known as WCry is now being used to carry out one of the biggest ransomware attacks of its kind. Visit this link to know everything about WanaCrypt0r Ransomware.
Well, it’s more than a week since this ransomware started causing distress among the internet users. However, it seems like security researchers are developing fixes for the Wannacry ransomware.
Previously, we have seen Adrien Guinet, a French security researcher from Quarkslab has found a cure to fix affected computers. Well, he discovered the fix for computers running Windows XP.
The researcher has succeeded to find the prime numbers that constitute the RSA private key used by WannaCry ransomware to crack the encryption process of WannaCry ransomware.
He uploaded WannaKey(tool) to his GitHub repo. He had open sourced the tool because he believed that other researcher might come up with a solution for other versions of Windows.
Now, another security researcher who goes by the name Benjamin Delpy has created another tool based on Adrien Guinet’s findings. He named the tool “WanaKiwi’ this tool can unlock the locked computer. This tool is compatible with Windows 7, Windows XP, Server 2003, Server 2008 and Vista.
Video Source: The Hacker News
WannaKiwi tool can run using the command prompt. If you are affected by the ransomware then you can download the tool from Github. So, what do you think about this? Share your views in the comment box below.

Comments
Post a Comment