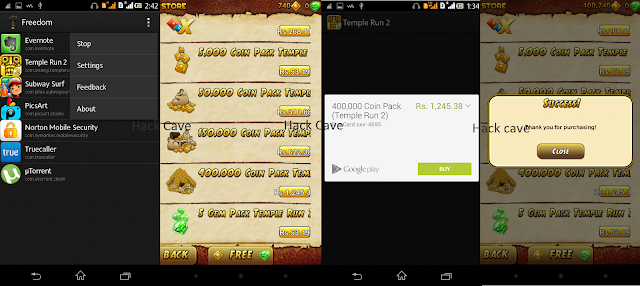
Hack Playstore - In App Purchases - In Android Easily |
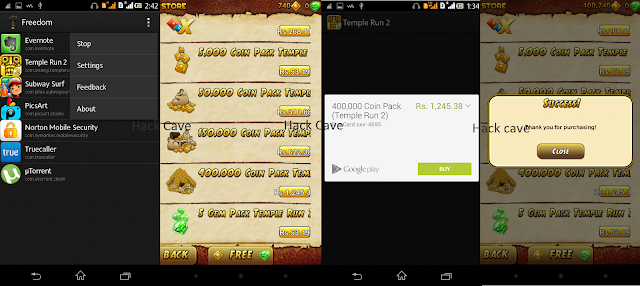
Freedom App:
- Freedom is an app which is used to hijack the PlayStore In-App purchases.
- In-App purchase is a feature by which a user can make purchases within the app.
- This comes in handy in situations like games and other apps which offer paid services.
- Freedom app contains an in-Built free card or credit card which it uses to make purchases on behalf of the user. One can get free coins, gems, lives, gold etc for free.
- It can be used to hack Subway Surfers, Hack Temple Run, and other android apps. Actual payment process gets taken over by freedom and in the end, the user gets the item which he/she bought without paying a single penny.
- To use the freedom app you need a rooted device. Procedure to use this app is simple. Download and install the app and let it run. Give root permissions when it asks.
- Then start the game and go to any purchase item option and click purchase. Now the Freedom app comes into the picture. It does the purchase and you will get the item for free.
For Download links and detailed step by step instructions.
Link in Comments,Check it out.

Link in Comments,Check it out.

Posted by Nagesh ;)

Comments
Post a Comment